Cybersecurity in Integrated IT Systems: Protecting Modern Digital Infrastructure
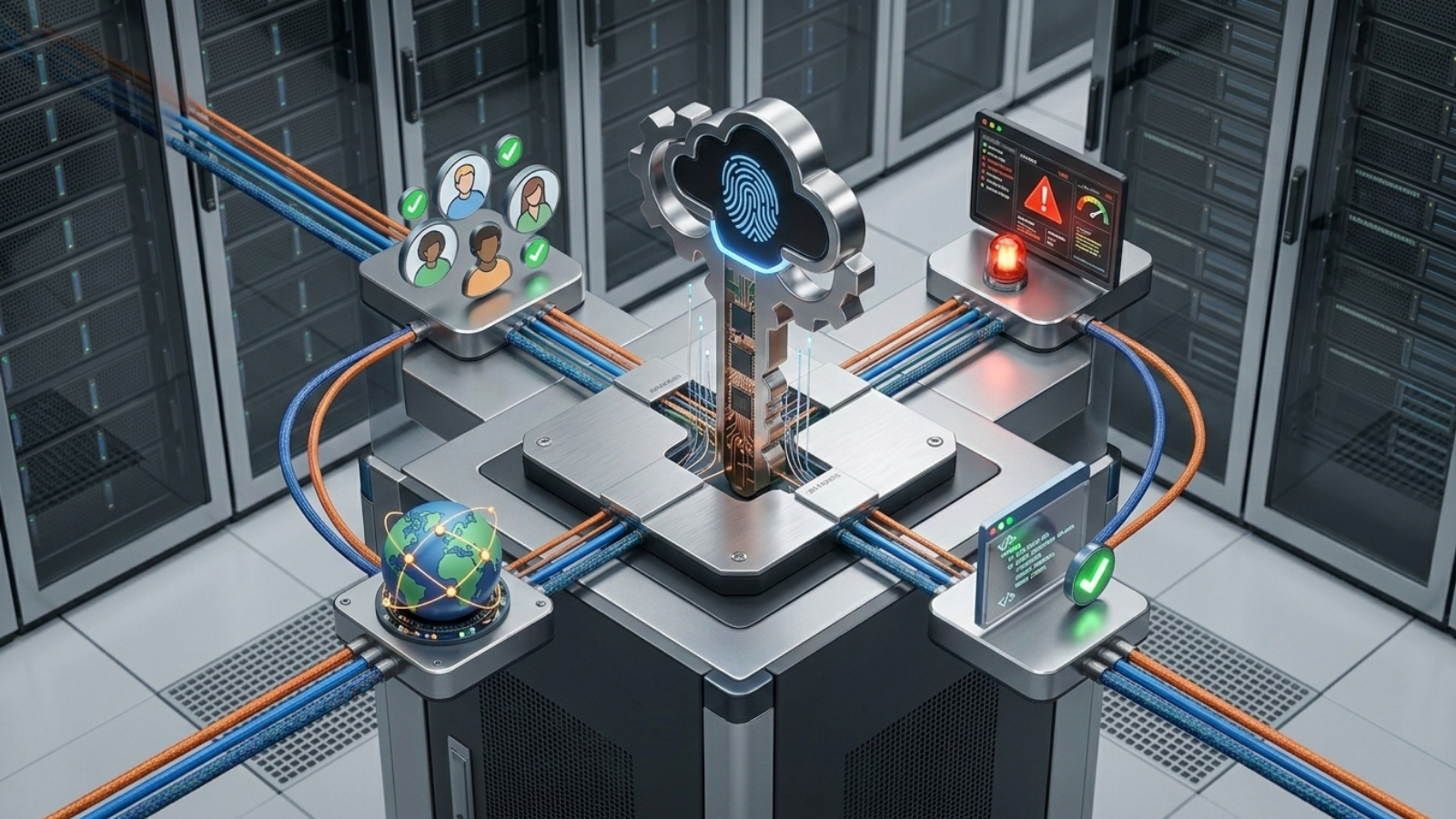
In today’s interconnected digital environment, cybersecurity has become a fundamental requirement for all integrated IT systems. As organizations adopt unified software and infrastructure architectures, the number of potential entry points for cyber threats also increases. This makes it essential to implement strong security frameworks that protect applications, networks, databases, and infrastructure layers as a single coordinated system. Cybersecurity is no longer an isolated function but a core component of system design.
In enterprise environments like DiginetSoft, cybersecurity is embedded directly into system architecture rather than added as an external layer. This ensures that every application, server, and network component follows strict security protocols from the initial design phase. By integrating security into infrastructure planning, organizations can reduce vulnerabilities, prevent unauthorized access, and maintain continuous system integrity across all operational layers.
Importance of Multi-Layer Security Architecture
Multi-layer security architecture is essential for protecting complex IT environments where multiple systems interact simultaneously. Instead of relying on a single point of defense, this approach creates multiple security barriers across application, network, and infrastructure levels. Each layer acts as an independent defense mechanism, ensuring that even if one layer is compromised, the overall system remains protected.
This layered approach significantly reduces the risk of data breaches, system intrusions, and unauthorized access attempts. It also allows security teams to monitor threats more effectively and respond to incidents in real time. As cyber threats continue to evolve, multi-layer security provides a scalable and adaptive defense strategy for modern enterprises.
Strong cybersecurity is not a feature — it is the foundation of every reliable digital system.
Role of Secure Infrastructure Design
Secure infrastructure design ensures that all hardware, software, and network components are built with security-first principles. This includes controlled access systems, encrypted communication channels, firewall protection, and continuous monitoring systems. By embedding security into infrastructure design, organizations can significantly reduce exposure to cyber risks.
Secure infrastructure also enables better compliance with industry regulations and data protection standards. It ensures that sensitive business and customer data is handled in a controlled and auditable environment. This not only protects against external threats but also minimizes internal security risks caused by human error or system misconfiguration.
Threat Detection and Real-Time Monitoring
Modern cybersecurity systems rely heavily on real-time monitoring and automated threat detection mechanisms. These systems continuously analyze network traffic, user behavior, and system activity to identify anomalies and potential security breaches. Early detection allows organizations to respond quickly and prevent damage before it escalates.
With advanced monitoring tools, security teams can gain complete visibility into system operations and detect suspicious patterns instantly. This proactive approach strengthens overall system resilience and ensures uninterrupted service availability even in high-risk environments.
Conclusion
Cybersecurity in integrated IT systems is a critical requirement for modern digital enterprises. As systems become more interconnected, the importance of strong, layered, and proactive security measures continues to grow. Organizations must treat cybersecurity as an integral part of system design rather than an external addition.
DiginetSoft’s approach to integrated cybersecurity ensures that software and infrastructure systems remain protected, resilient, and continuously monitored. This enables businesses to operate confidently in a secure digital environment while maintaining performance, scalability, and operational stability.



Leave a Reply